- Log in to:
- Community
- DigitalOcean
- Sign up for:
- Community
- DigitalOcean
By panosru
Hello, I need to open the ports 11443 and 11444 in order to be able to connect a desktop client with a web application, but even though that I set the rules properly to open the above-mentioned ports, they remain blocked.
My docker container also has the ports exposed:
root@docker-***:~# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
b1243cbeb471 idoop/zentao:latest "docker-entrypoint" 34 minutes ago Up 2 minutes (healthy) 80/tcp, 3306/tcp, 0.0.0.0:11443-11444->11443-11444/tcp zentao
The ports are set to be allowed in ufw:
root@docker-***:~# ufw status
Status: active
To Action From
-- ------ ----
22/tcp LIMIT Anywhere
2375/tcp ALLOW Anywhere
2376/tcp ALLOW Anywhere
11443/tcp ALLOW Anywhere
11444/tcp ALLOW Anywhere
22/tcp (v6) LIMIT Anywhere (v6)
2375/tcp (v6) ALLOW Anywhere (v6)
2376/tcp (v6) ALLOW Anywhere (v6)
11443/tcp (v6) ALLOW Anywhere (v6)
11444/tcp (v6) ALLOW Anywhere (v6)
Some additional info:
root@docker-***:~# netstat -plunt
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 951/sshd
tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN 699/systemd-resolve
tcp6 0 0 :::22 :::* LISTEN 951/sshd
tcp6 0 0 :::443 :::* LISTEN 1441/docker-proxy
tcp6 0 0 :::80 :::* LISTEN 1581/docker-proxy
tcp6 0 0 :::11443 :::* LISTEN 2349/docker-proxy
tcp6 0 0 :::11444 :::* LISTEN 1899/docker-proxy
udp 0 0 127.0.0.53:53 0.0.0.0:* 699/systemd-resolve
root@docker-***:~# iptables-save
# Generated by iptables-save v1.6.1 on Thu Jun 18 12:11:09 2020
*nat
:PREROUTING ACCEPT [88:5244]
:INPUT ACCEPT [50:2964]
:OUTPUT ACCEPT [82:6072]
:POSTROUTING ACCEPT [161:10036]
:DOCKER - [0:0]
-A PREROUTING -m addrtype --dst-type LOCAL -j DOCKER
-A OUTPUT ! -d 127.0.0.0/8 -m addrtype --dst-type LOCAL -j DOCKER
-A POSTROUTING -s 172.17.0.0/16 ! -o docker0 -j MASQUERADE
-A POSTROUTING -s 172.21.0.0/16 ! -o br-beef654e1741 -j MASQUERADE
-A POSTROUTING -s 172.19.0.0/16 ! -o br-a7d9c45b68cc -j MASQUERADE
-A POSTROUTING -s 172.19.0.17/32 -d 172.19.0.17/32 -p tcp -m tcp --dport 443 -j MASQUERADE
-A POSTROUTING -s 172.19.0.17/32 -d 172.19.0.17/32 -p tcp -m tcp --dport 80 -j MASQUERADE
-A POSTROUTING -s 172.19.0.22/32 -d 172.19.0.22/32 -p tcp -m tcp --dport 11444 -j MASQUERADE
-A POSTROUTING -s 172.19.0.22/32 -d 172.19.0.22/32 -p tcp -m tcp --dport 11443 -j MASQUERADE
-A DOCKER -i docker0 -j RETURN
-A DOCKER -i br-beef654e1741 -j RETURN
-A DOCKER -i br-a7d9c45b68cc -j RETURN
-A DOCKER ! -i br-a7d9c45b68cc -p tcp -m tcp --dport 443 -j DNAT --to-destination 172.19.0.17:443
-A DOCKER ! -i br-a7d9c45b68cc -p tcp -m tcp --dport 80 -j DNAT --to-destination 172.19.0.17:80
-A DOCKER ! -i br-a7d9c45b68cc -p tcp -m tcp --dport 11444 -j DNAT --to-destination 172.19.0.22:11444
-A DOCKER ! -i br-a7d9c45b68cc -p tcp -m tcp --dport 11443 -j DNAT --to-destination 172.19.0.22:11443
COMMIT
# Completed on Thu Jun 18 12:11:09 2020
# Generated by iptables-save v1.6.1 on Thu Jun 18 12:11:09 2020
*filter
:INPUT DROP [0:0]
:FORWARD DROP [0:0]
:OUTPUT ACCEPT [2:128]
:DOCKER - [0:0]
:DOCKER-ISOLATION-STAGE-1 - [0:0]
:DOCKER-ISOLATION-STAGE-2 - [0:0]
:DOCKER-USER - [0:0]
:ufw-after-forward - [0:0]
:ufw-after-input - [0:0]
:ufw-after-logging-forward - [0:0]
:ufw-after-logging-input - [0:0]
:ufw-after-logging-output - [0:0]
:ufw-after-output - [0:0]
:ufw-before-forward - [0:0]
:ufw-before-input - [0:0]
:ufw-before-logging-forward - [0:0]
:ufw-before-logging-input - [0:0]
:ufw-before-logging-output - [0:0]
:ufw-before-output - [0:0]
:ufw-logging-allow - [0:0]
:ufw-logging-deny - [0:0]
:ufw-not-local - [0:0]
:ufw-reject-forward - [0:0]
:ufw-reject-input - [0:0]
:ufw-reject-output - [0:0]
:ufw-skip-to-policy-forward - [0:0]
:ufw-skip-to-policy-input - [0:0]
:ufw-skip-to-policy-output - [0:0]
:ufw-track-forward - [0:0]
:ufw-track-input - [0:0]
:ufw-track-output - [0:0]
:ufw-user-forward - [0:0]
:ufw-user-input - [0:0]
:ufw-user-limit - [0:0]
:ufw-user-limit-accept - [0:0]
:ufw-user-logging-forward - [0:0]
:ufw-user-logging-input - [0:0]
:ufw-user-logging-output - [0:0]
:ufw-user-output - [0:0]
-A INPUT -j ufw-before-logging-input
-A INPUT -j ufw-before-input
-A INPUT -j ufw-after-input
-A INPUT -j ufw-after-logging-input
-A INPUT -j ufw-reject-input
-A INPUT -j ufw-track-input
-A FORWARD -j DOCKER-USER
-A FORWARD -j DOCKER-ISOLATION-STAGE-1
-A FORWARD -o docker0 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT
-A FORWARD -o docker0 -j DOCKER
-A FORWARD -i docker0 ! -o docker0 -j ACCEPT
-A FORWARD -i docker0 -o docker0 -j ACCEPT
-A FORWARD -o br-beef654e1741 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT
-A FORWARD -o br-beef654e1741 -j DOCKER
-A FORWARD -i br-beef654e1741 ! -o br-beef654e1741 -j ACCEPT
-A FORWARD -i br-beef654e1741 -o br-beef654e1741 -j ACCEPT
-A FORWARD -o br-a7d9c45b68cc -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT
-A FORWARD -o br-a7d9c45b68cc -j DOCKER
-A FORWARD -i br-a7d9c45b68cc ! -o br-a7d9c45b68cc -j ACCEPT
-A FORWARD -i br-a7d9c45b68cc -o br-a7d9c45b68cc -j ACCEPT
-A FORWARD -j ufw-before-logging-forward
-A FORWARD -j ufw-before-forward
-A FORWARD -j ufw-after-forward
-A FORWARD -j ufw-after-logging-forward
-A FORWARD -j ufw-reject-forward
-A FORWARD -j ufw-track-forward
-A OUTPUT -j ufw-before-logging-output
-A OUTPUT -j ufw-before-output
-A OUTPUT -j ufw-after-output
-A OUTPUT -j ufw-after-logging-output
-A OUTPUT -j ufw-reject-output
-A OUTPUT -j ufw-track-output
-A DOCKER -d 172.19.0.17/32 ! -i br-a7d9c45b68cc -o br-a7d9c45b68cc -p tcp -m tcp --dport 443 -j ACCEPT
-A DOCKER -d 172.19.0.17/32 ! -i br-a7d9c45b68cc -o br-a7d9c45b68cc -p tcp -m tcp --dport 80 -j ACCEPT
-A DOCKER -d 172.19.0.22/32 ! -i br-a7d9c45b68cc -o br-a7d9c45b68cc -p tcp -m tcp --dport 11444 -j ACCEPT
-A DOCKER -d 172.19.0.22/32 ! -i br-a7d9c45b68cc -o br-a7d9c45b68cc -p tcp -m tcp --dport 11443 -j ACCEPT
-A DOCKER-ISOLATION-STAGE-1 -i docker0 ! -o docker0 -j DOCKER-ISOLATION-STAGE-2
-A DOCKER-ISOLATION-STAGE-1 -i br-beef654e1741 ! -o br-beef654e1741 -j DOCKER-ISOLATION-STAGE-2
-A DOCKER-ISOLATION-STAGE-1 -i br-a7d9c45b68cc ! -o br-a7d9c45b68cc -j DOCKER-ISOLATION-STAGE-2
-A DOCKER-ISOLATION-STAGE-1 -j RETURN
-A DOCKER-ISOLATION-STAGE-2 -o docker0 -j DROP
-A DOCKER-ISOLATION-STAGE-2 -o br-beef654e1741 -j DROP
-A DOCKER-ISOLATION-STAGE-2 -o br-a7d9c45b68cc -j DROP
-A DOCKER-ISOLATION-STAGE-2 -j RETURN
-A DOCKER-USER -j RETURN
-A ufw-after-input -p udp -m udp --dport 137 -j ufw-skip-to-policy-input
-A ufw-after-input -p udp -m udp --dport 138 -j ufw-skip-to-policy-input
-A ufw-after-input -p tcp -m tcp --dport 139 -j ufw-skip-to-policy-input
-A ufw-after-input -p tcp -m tcp --dport 445 -j ufw-skip-to-policy-input
-A ufw-after-input -p udp -m udp --dport 67 -j ufw-skip-to-policy-input
-A ufw-after-input -p udp -m udp --dport 68 -j ufw-skip-to-policy-input
-A ufw-after-input -m addrtype --dst-type BROADCAST -j ufw-skip-to-policy-input
-A ufw-after-logging-input -m limit --limit 3/min --limit-burst 10 -j LOG --log-prefix "[UFW BLOCK] "
-A ufw-before-forward -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT
-A ufw-before-forward -p icmp -m icmp --icmp-type 3 -j ACCEPT
-A ufw-before-forward -p icmp -m icmp --icmp-type 4 -j ACCEPT
-A ufw-before-forward -p icmp -m icmp --icmp-type 11 -j ACCEPT
-A ufw-before-forward -p icmp -m icmp --icmp-type 12 -j ACCEPT
-A ufw-before-forward -p icmp -m icmp --icmp-type 8 -j ACCEPT
-A ufw-before-forward -j ufw-user-forward
-A ufw-before-input -i lo -j ACCEPT
-A ufw-before-input -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT
-A ufw-before-input -m conntrack --ctstate INVALID -j ufw-logging-deny
-A ufw-before-input -m conntrack --ctstate INVALID -j DROP
-A ufw-before-input -p icmp -m icmp --icmp-type 3 -j ACCEPT
-A ufw-before-input -p icmp -m icmp --icmp-type 4 -j ACCEPT
-A ufw-before-input -p icmp -m icmp --icmp-type 11 -j ACCEPT
-A ufw-before-input -p icmp -m icmp --icmp-type 12 -j ACCEPT
-A ufw-before-input -p icmp -m icmp --icmp-type 8 -j ACCEPT
-A ufw-before-input -p udp -m udp --sport 67 --dport 68 -j ACCEPT
-A ufw-before-input -j ufw-not-local
-A ufw-before-input -d 224.0.0.251/32 -p udp -m udp --dport 5353 -j ACCEPT
-A ufw-before-input -d 239.255.255.250/32 -p udp -m udp --dport 1900 -j ACCEPT
-A ufw-before-input -j ufw-user-input
-A ufw-before-output -o lo -j ACCEPT
-A ufw-before-output -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT
-A ufw-before-output -j ufw-user-output
-A ufw-logging-allow -m limit --limit 3/min --limit-burst 10 -j LOG --log-prefix "[UFW ALLOW] "
-A ufw-logging-deny -m conntrack --ctstate INVALID -m limit --limit 3/min --limit-burst 10 -j RETURN
-A ufw-logging-deny -m limit --limit 3/min --limit-burst 10 -j LOG --log-prefix "[UFW BLOCK] "
-A ufw-not-local -m addrtype --dst-type LOCAL -j RETURN
-A ufw-not-local -m addrtype --dst-type MULTICAST -j RETURN
-A ufw-not-local -m addrtype --dst-type BROADCAST -j RETURN
-A ufw-not-local -m limit --limit 3/min --limit-burst 10 -j ufw-logging-deny
-A ufw-not-local -j DROP
-A ufw-skip-to-policy-forward -j ACCEPT
-A ufw-skip-to-policy-input -j DROP
-A ufw-skip-to-policy-output -j ACCEPT
-A ufw-track-forward -p tcp -m conntrack --ctstate NEW -j ACCEPT
-A ufw-track-forward -p udp -m conntrack --ctstate NEW -j ACCEPT
-A ufw-track-output -p tcp -m conntrack --ctstate NEW -j ACCEPT
-A ufw-track-output -p udp -m conntrack --ctstate NEW -j ACCEPT
-A ufw-user-input -p tcp -m tcp --dport 22 -m conntrack --ctstate NEW -m recent --set --name DEFAULT --mask 255.255.255.255 --rsource
-A ufw-user-input -p tcp -m tcp --dport 22 -m conntrack --ctstate NEW -m recent --update --seconds 30 --hitcount 6 --name DEFAULT --mask 255.255.255.255 --rsource -j ufw-user-limit
-A ufw-user-input -p tcp -m tcp --dport 22 -j ufw-user-limit-accept
-A ufw-user-input -p tcp -m tcp --dport 2375 -j ACCEPT
-A ufw-user-input -p tcp -m tcp --dport 2376 -j ACCEPT
-A ufw-user-input -p tcp -m tcp --dport 11443 -j ACCEPT
-A ufw-user-input -p tcp -m tcp --dport 11444 -j ACCEPT
-A ufw-user-limit -m limit --limit 3/min -j LOG --log-prefix "[UFW LIMIT BLOCK] "
-A ufw-user-limit -j REJECT --reject-with icmp-port-unreachable
-A ufw-user-limit-accept -j ACCEPT
COMMIT
# Completed on Thu Jun 18 12:11:09 2020
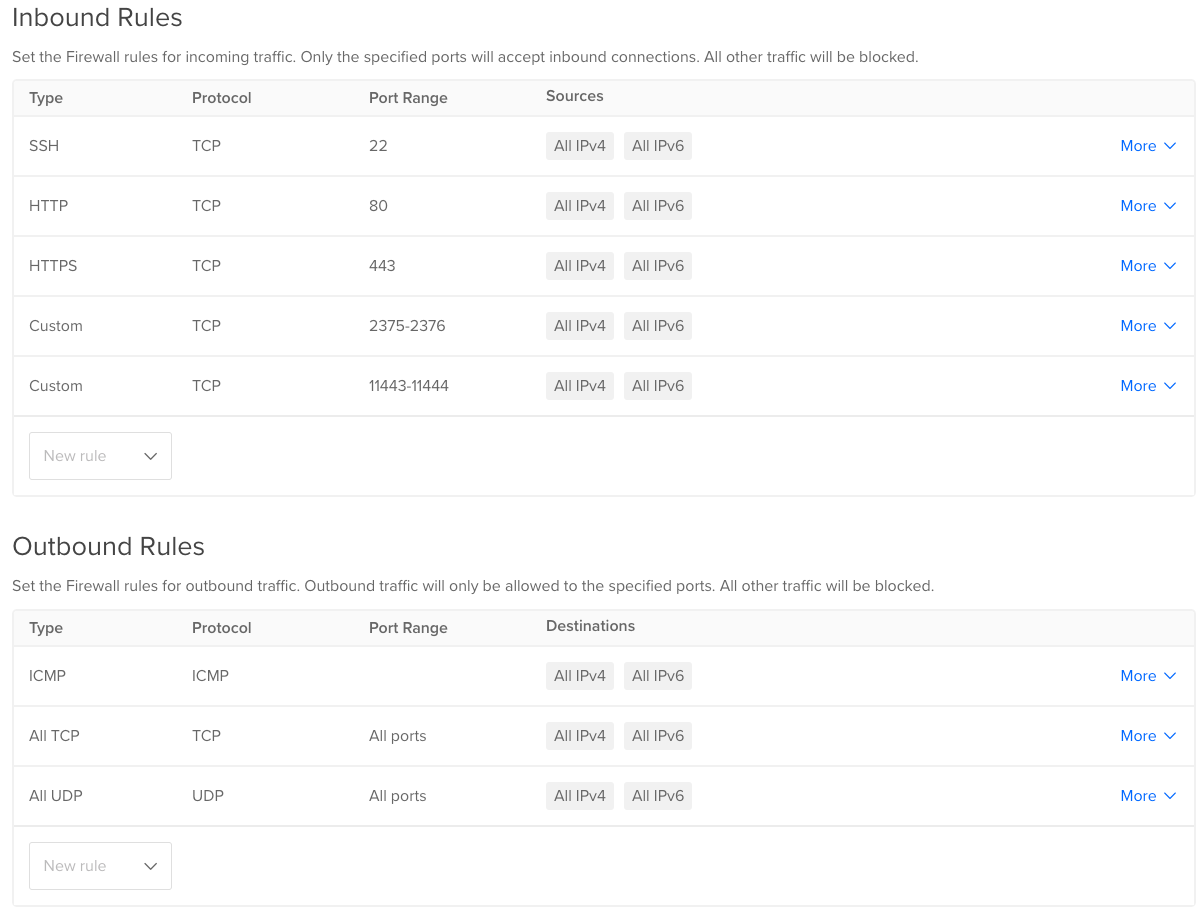
My DigitalOcean firewall settings look like this:
I’m also using Cloudflare, but I do not have the firewall enabled there.
Could anyone point me in the right direction on how to open the ports I need, because I’m out of ideas at that point?
Thanks!
This textbox defaults to using Markdown to format your answer.
You can type !ref in this text area to quickly search our full set of tutorials, documentation & marketplace offerings and insert the link!
Hi @panosru,
Looking at the provided information, you have allow only Ipv6 connections on ports 1143 and 1144.
root@docker-***:~# netstat -plunt
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 951/sshd
tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN 699/systemd-resolve
tcp6 0 0 :::22 :::* LISTEN 951/sshd
tcp6 0 0 :::443 :::* LISTEN 1441/docker-proxy
tcp6 0 0 :::80 :::* LISTEN 1581/docker-proxy
tcp6 0 0 :::11443 :::* LISTEN 2349/docker-proxy
tcp6 0 0 :::11444 :::* LISTEN 1899/docker-proxy
udp 0 0 127.0.0.53:53 0.0.0.0:* 699/systemd-resolve
If you look at the running application, it seems like the docker-proxy is only listening these ports on TCP6 - IPv6. This seems like you’ll need to update your app’s configuration so that it listens on the same ports but on IPv4.
Regards, KDSys
@KFSys, thank you for your response!
According to this similar to mine issue, I quote:
When setting up the proxy, Docker requests the loopback address ‘127.0.0.1’, Linux realises this is an address that exists in IPv6 (as ::0) and opens on both (but it is formally an IPv6 socket). When you run netstat it sees this and tells you it is an IPv6 - but it is still listening on IPv4. If you have played with your settings a little, you may have disabled this trick Linux does - by setting net.ipv6.bindv6only = 1.
Based on my settings:
root@docker-***:~# sysctl net.ipv6.bindv6only
net.ipv6.bindv6only = 0
I haven’t blocked this feature; thus, it seems to me that even though that netstat shows ipv6, docker container is still able to communicate on ipv4, no?
Sorry if I’m mistaken, I’m not a network expert, I’m just using Google a lot :)
Another person from the same StackOverflow issue, propose to set net.ipv6.conf.all.forwarding to 1, currently, I have it set to zero:
root@docker-tecfinity:~# sysctl net.ipv6.conf.all.forwarding
net.ipv6.conf.all.forwarding = 0
UPDATE:
I set net.ipv6.conf.all.forwarding to 1, but I still cannot access host:port from outside of local network.
I’m able to telnet from within the machine:
root@docker-***:~# telnet 127.0.0.1 11443
Trying 127.0.0.1...
Connected to 127.0.0.1.
Escape character is '^]'.
Connection closed by foreign host.
root@docker-***:~# telnet 127.0.0.1 11444
Trying 127.0.0.1...
Connected to 127.0.0.1.
Escape character is '^]'.
Connection closed by foreign host.
Some additional info:
root@docker-***:~# uname -a
Linux docker-*** 4.15.0-106-generic #107-Ubuntu SMP Thu Jun 4 11:27:52 UTC 2020 x86_64 x86_64 x86_64 GNU/Linux
root@docker-***:~# docker -v
Docker version 18.06.1-ce, build e68fc7a
root@docker-***:~# cat /etc/issue
Ubuntu 18.04.1 LTS \n \l
root@docker-***:~# iptables -t nat -nxvL
Chain PREROUTING (policy ACCEPT 26795 packets, 1604137 bytes)
pkts bytes target prot opt in out source destination
26505 1494209 DOCKER all -- * * 0.0.0.0/0 0.0.0.0/0 ADDRTYPE match dst-type LOCAL
Chain INPUT (policy ACCEPT 19106 packets, 1143013 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 7232 packets, 560351 bytes)
pkts bytes target prot opt in out source destination
0 0 DOCKER all -- * * 0.0.0.0/0 !127.0.0.0/8 ADDRTYPE match dst-type LOCAL
Chain POSTROUTING (policy ACCEPT 20817 packets, 1282907 bytes)
pkts bytes target prot opt in out source destination
0 0 MASQUERADE all -- * !docker0 172.17.0.0/16 0.0.0.0/0
0 0 MASQUERADE all -- * !br-beef654e1741 172.21.0.0/16 0.0.0.0/0
1438 86280 MASQUERADE all -- * !br-a7d9c45b68cc 172.19.0.0/16 0.0.0.0/0
0 0 MASQUERADE tcp -- * * 172.19.0.17 172.19.0.17 tcp dpt:443
0 0 MASQUERADE tcp -- * * 172.19.0.17 172.19.0.17 tcp dpt:80
0 0 MASQUERADE tcp -- * * 172.19.0.22 172.19.0.22 tcp dpt:11444
0 0 MASQUERADE tcp -- * * 172.19.0.22 172.19.0.22 tcp dpt:11443
Chain DOCKER (2 references)
pkts bytes target prot opt in out source destination
0 0 RETURN all -- docker0 * 0.0.0.0/0 0.0.0.0/0
0 0 RETURN all -- br-beef654e1741 * 0.0.0.0/0 0.0.0.0/0
0 0 RETURN all -- br-a7d9c45b68cc * 0.0.0.0/0 0.0.0.0/0
7025 333880 DNAT tcp -- !br-a7d9c45b68cc * 0.0.0.0/0 0.0.0.0/0 tcp dpt:443 to:172.19.0.17:443
336 15300 DNAT tcp -- !br-a7d9c45b68cc * 0.0.0.0/0 0.0.0.0/0 tcp dpt:80 to:172.19.0.17:80
1 40 DNAT tcp -- !br-a7d9c45b68cc * 0.0.0.0/0 0.0.0.0/0 tcp dpt:11444 to:172.19.0.22:11444
4 204 DNAT tcp -- !br-a7d9c45b68cc * 0.0.0.0/0 0.0.0.0/0 tcp dpt:11443 to:172.19.0.22:11443
UPDATE2:
I believe, that I’ll have to dig a bit in the container and make sure that the service that uses ports 11443-11444 is indeed working, I took it for granted but I have the suspicion that it may not.
Become a contributor for community
Get paid to write technical tutorials and select a tech-focused charity to receive a matching donation.
DigitalOcean Documentation
Full documentation for every DigitalOcean product.
Resources for startups and AI-native businesses
The Wave has everything you need to know about building a business, from raising funding to marketing your product.
Get our newsletter
Stay up to date by signing up for DigitalOcean’s Infrastructure as a Newsletter.
New accounts only. By submitting your email you agree to our Privacy Policy
The developer cloud
Scale up as you grow — whether you're running one virtual machine or ten thousand.
Get started for free
Sign up and get $200 in credit for your first 60 days with DigitalOcean.*
*This promotional offer applies to new accounts only.