- Log in to:
- Community
- DigitalOcean
- Sign up for:
- Community
- DigitalOcean
By Bulat Khamitov
Not using Ubuntu 12.04?
Choose a different version or distribution.
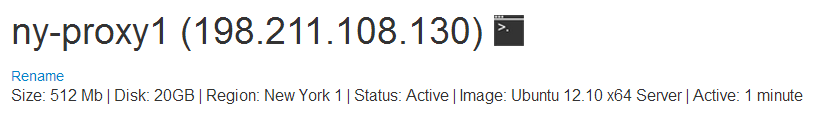
Step 1 - Spin up a Ubuntu 12.10 x64 droplet
Step 2 - Install Squid
apt-get install -y squid update-rc.d squid3 defaults
Step 3 - Setup Access Restrictions
Since this Squid proxy would allow anyone using it to make connections from your droplet's IP address, you would want to restrict access to it.
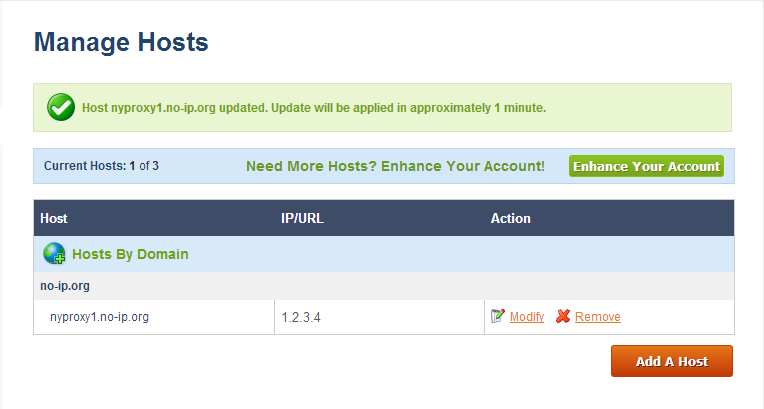
You can register a free dynamic IP from services like noip.com
If you would like to use this Squid proxy from your phone, you would have to install a dynamic DNS update client.
You can use applications like Dynamic DNS Client for Android, or FreeDynPro for iOS
.
Once you have a dynamic IP hostname, you can update it from your router at home, mobile device, or an API call.
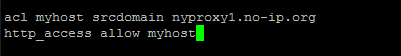
This hostname should be added to /etc/squid3/squid.conf. Edit the file and add your hostname (nyproxy1.no-ip.org in our case):
acl myhost srcdomain nyproxy1.no-ip.org http_access allow myhost
Setup a crontab that reloads Squid every hour, in case your IP address changes:
echo 0 */1 * * * service squid3 reload >> /var/spool/cron/root
Step 4 - Configure Squid Proxy
By default, Squid listens on port 3128. If you would like to use a different port, modify /etc/squid3/squid.conf
http_port 3128
If you would like to browse through this Squid proxy and not have it detected as a proxy, setup anonymous settings by adding these lines to /etc/squid3/squid.conf:
via off forwarded_for off request_header_access Allow allow all request_header_access Authorization allow all request_header_access WWW-Authenticate allow all request_header_access Proxy-Authorization allow all request_header_access Proxy-Authenticate allow all request_header_access Cache-Control allow all request_header_access Content-Encoding allow all request_header_access Content-Length allow all request_header_access Content-Type allow all request_header_access Date allow all request_header_access Expires allow all request_header_access Host allow all request_header_access If-Modified-Since allow all request_header_access Last-Modified allow all request_header_access Location allow all request_header_access Pragma allow all request_header_access Accept allow all request_header_access Accept-Charset allow all request_header_access Accept-Encoding allow all request_header_access Accept-Language allow all request_header_access Content-Language allow all request_header_access Mime-Version allow all request_header_access Retry-After allow all request_header_access Title allow all request_header_access Connection allow all request_header_access Proxy-Connection allow all request_header_access User-Agent allow all request_header_access Cookie allow all request_header_access All deny all
Step 5 - Start Squid proxy service
service squid3 start
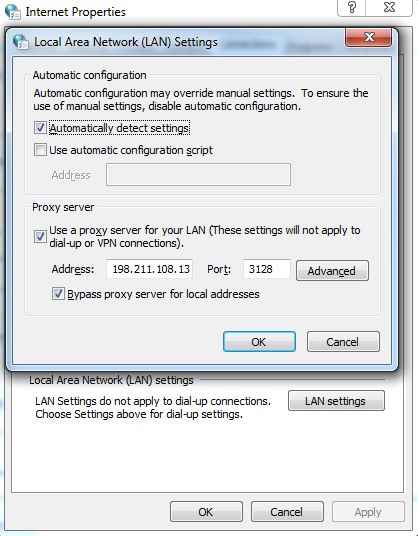
Step 6 - Modify your browser's proxy settings
Step 7 - Verify Squid proxy works
Navigate over to whatismyip.com
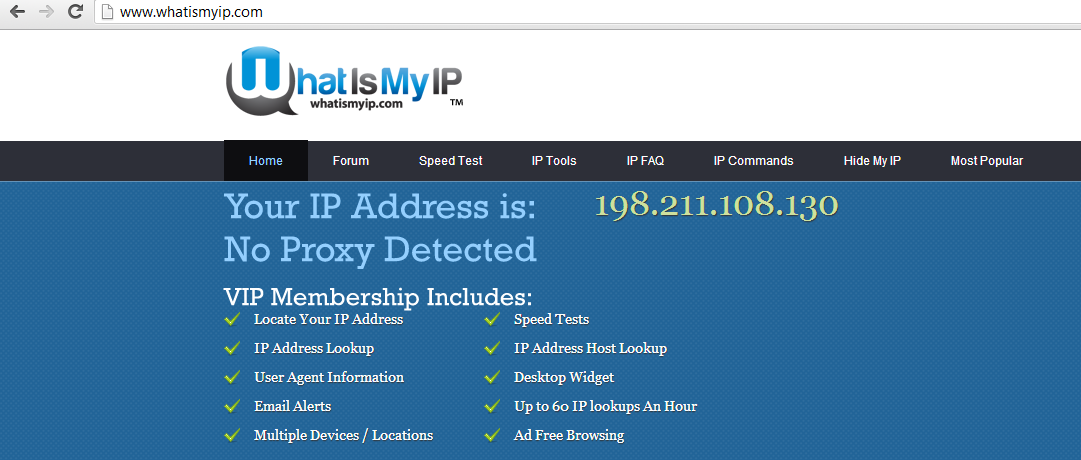
And you are all done!
Thanks for learning with the DigitalOcean Community. Check out our offerings for compute, storage, networking, and managed databases.
Still looking for an answer?
This textbox defaults to using Markdown to format your answer.
You can type !ref in this text area to quickly search our full set of tutorials, documentation & marketplace offerings and insert the link!
Can’t we setup a proxy with user names and passwords? Plus how can we determine how much bandwidth is used per account?
htpasswd /etc/squid/passwd user1
chmod o+r /etc/squid/passwd
Locate ncsa_auth module
dpkg -L squid | grep ncsa_auth
cat /etc/squid/squid.conf
auth_param basic program /usr/lib/squid/ncsa_auth /etc/squid/passwd auth_param basic children 5 auth_param basic realm Squid Proxy auth_param basic credentialsttl 2 hours auth_param basic casesensitive off —skipped— acl ncsa_users proxy_auth REQUIRED http_access allow ncsa_users
thanks but editing the conf was a little difficult so i had to refer to experts-exchange.com maybe you can borrow some material from there http://www.experts-exchange.com/OS/Linux/Q_23064565.html
Can anyone tell me how to setup a server with proxy authentication. Like we have a network which uses proxy with authentication. Need to configure squid so that, we can give this machine one which we have created squid and use internet on other machines directly. Let us know.
Thank you in advance.
@rajhanschinmay: Take a look at this post:
hey there, i have squid3 on ubuntu 12_10 64bit and my config looks like this:
http_port 3128
auth_param basic program /usr/lib/squid3/ncsa_auth /etc/squid3/passwd auth_param basic children 5 auth_param basic realm Squid proxy-caching webserver auth_param basic credentialsttl 2 hours
acl ncsaauth proxy_auth REQUIRED http_access allow ncsaauth
but whatever i try, i cannot connect to it, there is no login promt and nothing in my browser when i want to connect to the proxy.
and for the error log…looks like:
2013/09/24 17:46:53| Starting Squid Cache version 3.1.20 for x86_64-pc-linux-gnu… 2013/09/24 17:46:53| Process ID 2401 2013/09/24 17:46:53| With 65535 file descriptors available 2013/09/24 17:46:53| Initializing IP Cache… 2013/09/24 17:46:53| DNS Socket created at [::], FD 5 2013/09/24 17:46:53| DNS Socket created at 0.0.0.0, FD 6 2013/09/24 17:46:53| Adding nameserver 4.2.2.2 from /etc/resolv.conf 2013/09/24 17:46:53| Adding nameserver 8.8.8.8 from /etc/resolv.conf 2013/09/24 17:46:53| helperOpenServers: Starting 5/5 ‘ncsa_auth’ processes 2013/09/24 17:46:54| Unlinkd pipe opened on FD 21 2013/09/24 17:46:54| Local cache digest enabled; rebuild/rewrite every 3600/3600 sec 2013/09/24 17:46:54| Store logging disabled 2013/09/24 17:46:54| Swap maxSize 0 + 262144 KB, estimated 20164 objects 2013/09/24 17:46:54| Target number of buckets: 1008 2013/09/24 17:46:54| Using 8192 Store buckets 2013/09/24 17:46:54| Max Mem size: 262144 KB 2013/09/24 17:46:54| Max Swap size: 0 KB 2013/09/24 17:46:54| Using Least Load store dir selection 2013/09/24 17:46:54| Current Directory is / 2013/09/24 17:46:54| Loaded Icons. 2013/09/24 17:46:54| Accepting HTTP connections at [::]:3128, FD 22. 2013/09/24 17:46:54| HTCP Disabled. 2013/09/24 17:46:54| Squid plugin modules loaded: 0 2013/09/24 17:46:54| Adaptation support is off. 2013/09/24 17:46:54| Ready to serve requests. 2013/09/24 17:46:55| storeLateRelease: released 0 objects 2013/09/24 17:47:19| Preparing for shutdown after 0 requests 2013/09/24 17:47:19| Waiting 30 seconds for active connections to finish
anyone some ideas?
hey,
This tutorial has not been working for me… every time i tried to load a web page in the log (on the server) i got: TCP_DENIED/403 for every request i made with my computer. and what was shown in my computer was: “Access control configuration prevents your request from being allowed at this time. Please contact your service provider if you feel this is incorrect.”
what should i do to get past this problem?
thanks, eliran.
@eliran: What’s the output of <pre>cat /etc/squid3/squid.conf | grep acl</pre>?
Please help someone! I am facing following problem after installing squid proxy and also I am not able to configure Host via noip.com as When I run that command it’s shows me command not found and also I am not able to run Step4 commands - it says that command not found.
However after starting up squid proxy service and setting it up to my browser, it’s showing me following in my browser while opening any website:
_______________________________________________________________________________________-
ERROR
The requested URL could not be retrieved
The following error was encountered while trying to retrieve the URL: http://google.com/
Access Denied.
Access control configuration prevents your request from being allowed at this time. Please contact your service provider if you feel this is incorrect.
Your cache administrator is webmaster.
Generated Tue, 04 Feb 2014 19:11:17 GMT by localhost (squid/3.1.20)
- Table of contents
Deploy on DigitalOcean
Click below to sign up for DigitalOcean's virtual machines, Databases, and AIML products.
Become a contributor for community
Get paid to write technical tutorials and select a tech-focused charity to receive a matching donation.
DigitalOcean Documentation
Full documentation for every DigitalOcean product.
Resources for startups and AI-native businesses
The Wave has everything you need to know about building a business, from raising funding to marketing your product.
Get our newsletter
Stay up to date by signing up for DigitalOcean’s Infrastructure as a Newsletter.
New accounts only. By submitting your email you agree to our Privacy Policy
The developer cloud
Scale up as you grow — whether you're running one virtual machine or ten thousand.
Start building today
From GPU-powered inference and Kubernetes to managed databases and storage, get everything you need to build, scale, and deploy intelligent applications.
