- Log in to:
- Community
- DigitalOcean
- Sign up for:
- Community
- DigitalOcean

Introduction
Linux offers a wide range of powerful command-line tools that are available out of the box in most distributions. Among these, Netcat stands out as a versatile networking utility that enables direct interaction with remote systems using TCP or UDP protocols. System administrators and developers alike can use Netcat for everything from port scanning and service testing to file transfers and debugging.
In this comprehensive guide, you’ll learn how to use Netcat to establish and test TCP and UDP connections in practical scenarios. We’ll explore how Netcat can be used to send and receive data, scan for open ports, troubleshoot connectivity issues, and even set up simple chat servers or ad hoc file transfers. Along the way, we’ll cover variant differences (nc, ncat, netcat-openbsd), dive into real-time debugging techniques, interpret silent failures (especially over UDP), and compare Netcat with modern alternatives like telnet and socat.
Key takeaways
- Netcat is a versatile networking tool that allows you to establish TCP and UDP connections, making it useful for testing, debugging, and transferring data between systems.
- Basic usage includes connecting to ports, scanning ranges, and sending raw data, with support for options like
-u(UDP),-z(scan-only), and-v(verbose output). - Netcat can act as both client and server, enabling bi-directional communication, file transfers, and even simple chat sessions or web servers using shell piping.
- There are multiple versions of Netcat, including
netcat-openbsd,nc, andncat, each with different features and behavior. Knowing which one you’re using is critical for consistent results. - Netcat is a valuable debugging tool, allowing you to manually send HTTP headers, inspect service banners, and simulate client behavior for protocols like SMTP, DNS, and HTTP.
- UDP behavior can be hard to interpret, as Netcat does not confirm delivery or receipt. Use tools like
tcpdumpto monitor traffic and validate connectivity. - Netcat isn’t always the best tool for the job; modern tools like
socatoffer more advanced functionality, whiletelnetmay suffice for simple TCP testing.
General Syntax
By default, netcat operates by initiating a TCP connection to a remote host.
The most basic syntax is:
- netcat [options] host port
This will attempt to initiate a TCP connection to the defined host on the port number specified. This functions similarly to the old Linux telnet command. Keep in mind that your connection is entirely unencrypted.
If you would like to send a UDP packet instead of initiating a TCP connection, you can use the -u option:
- netcat -u host port
You can specify a range of ports by placing a dash between the first and last:
- netcat host startport-endport
This is generally used with some additional flags.
On many systems, nc is a symbolic link to a Netcat variant like netcat-openbsd or ncat, so while the names are used interchangeably, behavior may vary across platforms.
What are the differences between nc, ncat, and netcat-openbsd?
nc, ncat, and netcat-openbsd?Although they share a common purpose, not all versions of Netcat behave the same way. Depending on your operating system and installed packages, you may encounter different implementations of Netcat, each with its own feature set and quirks. Understanding these differences can help you avoid confusion when working across environments.
netcat-openbsd
This is the default Netcat version on most Debian-based systems such as Ubuntu. It is a modern and actively maintained version derived from the OpenBSD project, and it supports many helpful options including:
-wfor connection timeouts-zfor scan-only mode (no data transfer)-nto prevent DNS resolution-ufor UDP mode- IPv6 support (
-6)
This version is considered feature-rich and is the most commonly used variant in Linux tutorials and documentation. If you’re using Ubuntu, you’re likely already using netcat-openbsd.
To install it explicitly:
- sudo apt install netcat-openbsd
nc
The nc command is not a standalone utility on its own, but rather an alias or symbolic link that points to one of the available Netcat variants on your system. In most distributions, you can use nc and netcat interchangeably:
- which nc
- ls -l $(which nc)
This will help you determine which version your nc command is actually invoking. Always check this when working in a new environment to avoid unintended behavior.
ncat
ncat is a complete rewrite of Netcat developed by the Nmap project. It is the default Netcat utility on CentOS, Fedora, RHEL, and other Red Hat-based distributions. Compared to traditional Netcat versions, ncat provides a wider range of features, including:
- SSL encryption (
--ssl) - Connection brokering (
--broker) - HTTP proxy support (
--proxy) - Input/output redirection similar to Unix-style tools
For example, to encrypt a Netcat session using SSL with ncat:
- ncat --ssl -l 4444
Keep in mind that some common flags like -z or -e may behave differently or be disabled entirely in ncat for security reasons.
How to use Netcat for port scanning
One of the most common uses for netcat is as a port scanner.
Although netcat is probably not the most sophisticated tool for the job (nmap is a better choice in most cases), it can perform simple port scans to easily identify open ports.
We do this by specifying a range of ports to scan, as we did above, along with the -z option to perform a scan instead of attempting to initiate a connection.
For instance, we can scan all ports up to 1000 by issuing this command:
- netcat -z -v domain.com 1-1000
Along with the -z option, we have also specified the -v option to tell netcat to provide more verbose information.
The output will look like this:
Outputnc: connect to domain.com port 1 (tcp) failed: Connection refused
nc: connect to domain.com port 2 (tcp) failed: Connection refused
nc: connect to domain.com port 3 (tcp) failed: Connection refused
nc: connect to domain.com port 4 (tcp) failed: Connection refused
nc: connect to domain.com port 5 (tcp) failed: Connection refused
nc: connect to domain.com port 6 (tcp) failed: Connection refused
nc: connect to domain.com port 7 (tcp) failed: Connection refused
. . .
Connection to domain.com 22 port [tcp/ssh] succeeded!
. . .
As you can see, this provides a lot of information and will tell you for each port whether a scan was successful or not.
If you are actually using a domain name, this is the form you will have to use.
However, your scan will go much faster if you know the IP address that you need. You can then use the -n flag to specify that you do not need to resolve the IP address using DNS:
- netcat -z -n -v 198.51.100.0 1-1000
The messages returned are actually sent to standard error (see our I/O redirection article for more info). We can send the standard error messages to standard output, which will allow us to filter the results easier.
We will redirect standard error to standard output using the 2>&1 bash syntax. We will then filter the results with grep:
- netcat -z -n -v 198.51.100.0 1-1000 2>&1 | grep succeeded
OutputConnection to 198.51.100.0 22 port [tcp/*] succeeded!
Here, we can see that the only port open in the range of 1–1000 on the remote computer is port 22, the traditional SSH port.
How to communicate through Netcat
Netcat is not restricted to sending TCP and UDP packets. It also can listen on a port for connections and packets. This gives us the opportunity to connect two instances of netcat in a client-server relationship.
Which computer is the server and which is the client is only a relevant distinction during the initial configuration. After the connection is established, communication is exactly the same in both directions.
On one machine, you can tell netcat to listen to a specific port for connections. We can do this by providing the -l parameter and choosing a port:
- netcat -l 4444
This will tell netcat to listen for TCP connections on port 4444. As a regular (non-root) user, you will not be able to open any ports under 1024, as a security measure.
On a second server, we can connect to the first machine on the port number we chose. We do this the same way we’ve been establishing connections previously:
- netcat domain.com 4444
It will look as if nothing has happened. However, you can now send messages on either side of the connection and they will be seen on either end.
Type a message and press ENTER. It will appear on both the local and remote screen. This works in the opposite direction as well.
When you are finished passing messages, you can press CTRL-D to close the TCP connection.
How to use Netcat in real-time debugging scenarios
Netcat is a powerful utility for low-level interaction with network services. System administrators and developers can use it to quickly inspect service availability, test raw protocol communication, and analyze how services respond to specific inputs. This makes Netcat an ideal tool for real-time debugging of services like HTTP, SMTP, and DNS.
Viewing Service Banners
Many TCP services send a short message immediately after a connection is established. This is known as a banner, and it often contains version information or a greeting from the service.
To view the banner from an SMTP mail server:
- nc mail.example.com 25
Output220 mail.example.com ESMTP Postfix
This confirms that the SMTP server is accessible and functioning. Similar banners can be observed for FTP (port 21), POP3 (port 110), and other protocol-based services.
Testing HTTP Responses Manually
You can also use Netcat to manually send HTTP requests and inspect how a web server responds. This is particularly helpful for debugging load balancer behavior, reverse proxy routing, or HTTP headers.
- printf "GET / HTTP/1.1\r\nHost: example.com\r\n\r\n" | nc example.com 80
This sends a basic GET request with a Host header, just like a browser would. The server will respond with raw HTTP headers and content, allowing you to confirm:
- HTTP status codes (e.g.,
200 OK,404 Not Found) - Server type and version
- Content-Type headers
- Caching behavior
This method is useful when you need to test a service without using a browser or more complex tools like curl.
Debugging Custom Protocols or Services
For internal services, Netcat lets you quickly simulate a client connection to check that the server responds as expected. This can help uncover misconfigured firewalls, broken routing rules, or application-level issues during initial setup.
By typing directly into the connection, you can observe how the server reacts to different inputs. This raw control over input/output is one of Netcat’s biggest advantages for real-time debugging.
How To Send Files through Netcat
Building off of the previous example, we can accomplish more useful tasks.
Because we are establishing a regular TCP connection, we can transmit just about any kind of information over that connection. It is not limited to chat messages that are typed in by a user. We can use this knowledge to turn netcat into a file transfer program.
Once again, we need to choose one end of the connection to listen for connections. However, instead of printing information onto the screen, as we did in the last example, we will place all of the information straight into a file:
- netcat -l 4444 > received_file
The > in this command redirects all the output of netcat into the specified filename.
On the second computer, create a simple text file by typing:
- echo "Hello, this is a file" > original_file
We can now use this file as an input for the netcat connection we will establish to the listening computer. The file will be transmitted just as if we had typed it interactively:
- netcat domain.com 4444 < original_file
We can see on the computer that was awaiting a connection, that we now have a new file called received_file with the contents of the file we typed on the other computer:
- cat received_file
OutputHello, this is a file
As you can see, by piping things, we can easily take advantage of this connection to transfer all kinds of things.
For instance, we can transfer the contents of an entire directory by creating an unnamed tarball on-the-fly, transferring it to the remote system, and unpacking it into the remote directory.
On the receiving end, we can anticipate a file coming over that will need to be unzipped and extracted by typing:
- netcat -l 4444 | tar xzvf -
The ending dash (-) means that tar will operate on standard input, which is being piped from netcat across the network when a connection is made.
On the side with the directory contents we want to transfer, we can pack them into a tarball and then send them to the remote computer through netcat:
- tar -czf - * | netcat domain.com 4444
This time, the dash in the tar command means to tar and zip the contents of the current directory (as specified by the * wildcard), and write the result to standard output.
This is then written directly to the TCP connection, which is then received at the other end and decompressed into the current directory of the remote computer.
This is just one example of transferring more complex data from one computer to another. Another common idea is to use the dd command to image a disk on one side and transfer it to a remote computer. We won’t be covering this here though.
How To Use Netcat as a Simple Web Server
We’ve been configuring netcat to listen for connections in order to communicate and transfer files. We can use this same concept to operate netcat as a very simple web server. This can be useful for testing pages that you are creating.
First, let’s make a simple HTML file on one server:
- nano index.html
Here is some simple HTML that you can use in your file:
<html>
<head>
<title>Test Page</title>
</head>
<body>
<h1>Level 1 header</h1>
<h2>Subheading</h2>
<p>Normal text here</p>
</body>
</html>
Save and close the file.
Without root privileges, you cannot serve this file on the default web port, port 80. We can choose port 8888 as a regular user.
If you just want to serve this page one time to check how it renders, you can run the following command:
- (echo -e "HTTP/1.1 200 OK\r\nContent-Type: text/html\r\n\r\n"; cat index.html) | netcat -l 8888
Now, in your browser, you can access the content by visiting:
http://server_IP:8888
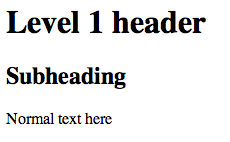
This will serve the page, and then the netcat connection will close. If you attempt to refresh the page, it will be gone:

We can have netcat serve the page indefinitely by wrapping the last command in an infinite loop, like this:
- while true; do printf 'HTTP/1.1 200 OK\n\n%s' "$(cat index.html)" | netcat -l 8888; done
This will allow it to continue to receive connections after the first connection closes.
We can stop the loop by typing CTRL-C on the server.
This allows you to see how a page renders in a browser, but it doesn’t provide much more functionality. You should never use this for serving actual websites. There is no security and simple things like links do not even work correctly.
Interpreting No Output or Connection Timeouts (Especially for UDP)
One of the challenges when using Netcat is knowing what to expect from the output. Netcat is intentionally minimal, which means a lack of output can sometimes be confusing, especially when working with UDP or interacting with silent services.
Understanding TCP Silence
If you attempt to connect to a TCP service using Netcat and the terminal appears to do nothing, this usually means that the connection was successful, but the service is waiting for input.
For example:
- nc example.com 22
If the server doesn’t send a banner immediately (as is the case with some custom services), you won’t see any output. You can test interaction by typing something and pressing ENTER.
On the other hand, if the connection fails outright, Netcat will return an error like:
nc: connect to example.com port 22 (tcp) failed: Connection refused
This indicates that the port is either closed or blocked by a firewall.
Dealing with UDP Silence
UDP is a connectionless protocol, which makes troubleshooting more difficult. When you send a UDP packet using Netcat, you will often receive no confirmation that the packet was delivered, processed, or rejected.
Example:
- nc -u example.com 53
Even if a DNS server is listening on port 53, Netcat may display no output at all, especially if the packet format is invalid.
This silence is expected behavior with UDP. Unlike TCP, there is no handshake, no acknowledgment, and often no error message.
How to Diagnose UDP Issues
If you’re unsure whether Netcat is working over UDP, here are a few ways to troubleshoot:
- Add verbosity: Use
-vto show more information during the connection attempt. - Use packet capture tools: Use
tcpdumporWiresharkto inspect whether packets are being sent and received. - Ensure proper formatting: Some services (like DNS) expect a specific binary packet structure. Netcat won’t construct these automatically.
Netcat is a helpful first step for probing UDP ports, but deeper debugging may require protocol-specific tools like dig, tshark, or iperf.
Comparing Netcat with Modern Tools Like socat or telnet
socat or telnetNetcat is extremely powerful for many ad hoc networking tasks, but it is not always the most suitable tool. Depending on your use case, newer or more specialized tools like socat or telnet may offer capabilities that better fit your needs.
Netcat vs. Telnet
The telnet command is often used to test basic TCP connectivity and interact with services like HTTP, SMTP, or FTP.
- telnet example.com 80
Once connected, you can type requests manually and view the server’s response. This is similar to Netcat, but there are some key differences:
| Feature | Telnet | Netcat |
|---|---|---|
| TCP Support | Yes | Yes |
| UDP Support | No | Yes |
| Output echo | Yes | No (by default) |
| Scripting Support | Limited | Extensive |
| Deprecated Status | Obsolete on many systems | Actively used |
Telnet automatically echoes your keystrokes, which can be convenient, but it lacks the flexibility and scripting capabilities that Netcat offers. Additionally, Telnet has mostly been phased out on modern systems due to security concerns and limited protocol support.
Netcat vs. Socat
socat (SOcket CAT) is a more sophisticated and configurable tool that expands on the capabilities of Netcat. While Netcat connects two endpoints directly, Socat provides more flexibility by linking two arbitary data streams such as sockets, files, or devices.
For example, you can transfer a file over TCP using socat:
- socat FILE:myfile TCP:example.com:4444
Or you can forward a TCP connection over an SSL tunnel:
- socat TCP-LISTEN:443,reuseaddr,fork SSL:remote.example.com:443,verify=0
Key features of socat:
- Full duplex communication
- SSL/TLS support
- IPv6 compatibility
- Support for serial devices, proxies, and more
Because of its complexity, socat has a steeper learning curve, but it is ideal for advanced networking scenarios and production use cases where Netcat’s simplicity becomes a limitation.
How to troubleshoot common Netcat errors and issues
While Netcat is generally a lightweight and reliable tool, it can produce confusing behavior when something goes wrong. Because it does not output much by default, identifying issues may require understanding how Netcat handles connections, data, and protocols.
Here are some common problems you may encounter and how to troubleshoot them effectively.
“Connection Refused” Errors
If Netcat fails to establish a TCP connection and you see an error like:
nc: connect to example.com port 4444 (tcp) failed: Connection refused
This typically indicates one of the following:
- The remote port is closed: The target server is not listening on the specified port.
- The service is not running: For example, if you are testing a web server on port
80, confirm that the web server is active. - Firewall rules are blocking the connection: Either the source or destination system may have a firewall that is rejecting the traffic.
How to fix it:
-
Verify the target service is running and bound to the correct port:
- sudo netstat -tulpn | grep 4444
-
Check firewall rules on both systems:
- sudo ufw status
- sudo iptables -L
-
Try connecting to a different known-open port (like
22for SSH) to verify basic connectivity.
“No Route to Host” or “Network is Unreachable”
If Netcat fails with an error like:
nc: connect to example.com port 4444 (tcp) failed: No route to host
This typically suggests a network-level problem: Netcat cannot reach the destination IP or hostname.
Possible causes include:
- Incorrect IP address or DNS resolution failure
- Missing or misconfigured default gateway
- Dropped packets or blocked ICMP on routers or firewalls
How to fix it:
-
Test connectivity using
pingortraceroute:- ping example.com
- traceroute example.com
-
Check DNS resolution:
- nslookup example.com
- dig example.com
-
Confirm you’re on the correct network or VPN, especially when working in cloud environments.
Nothing Happens After Connecting
In many cases, you may successfully connect to a TCP port using Netcat, but nothing appears on the screen and the terminal seems to freeze. This can be misleading if you’re expecting immediate output.
This behavior usually means:
- The TCP connection is established, but the server is waiting for input.
- The remote service does not provide a banner or initial message.
- You’ve connected to the wrong service type for that port.
How to fix it:
-
Type something and press
ENTERto see if the service responds. -
Try a protocol-appropriate payload, such as an HTTP
HEADrequest for web servers:- printf "HEAD / HTTP/1.1\r\nHost: example.com\r\n\r\n" | nc example.com 80
-
Use the
-v(verbose) flag to get feedback on connection status:- nc -v example.com 80
No Response When Using UDP
As covered earlier, Netcat does not guarantee a response when sending UDP packets. This can cause confusion during testing.
Possible explanations:
- The remote service only responds to properly structured UDP packets (e.g., a DNS query).
- The packet was received but dropped due to invalid format or security filters.
- There is no service listening on the remote UDP port.
How to fix it:
-
Confirm the service supports UDP and is actively listening.
-
Use packet capture tools like
tcpdumpto verify transmission:- sudo tcpdump -n udp port 53
-
Try using application-specific tools (e.g.,
digfor DNS,iperffor UDP throughput testing) if Netcat is too low-level.
“bind: Address already in use” When Listening
When running Netcat in listening mode with -l, you may encounter:
nc: bind: Address already in use
This happens when another process is already listening on the same port.
How to fix it:
-
Find the process using the port:
- sudo lsof -i :4444
-
Terminate the conflicting process if it’s not needed:
- sudo kill -9 <PID>
-
Or, simply choose a different port (above 1024 if not running as root).
Netcat Hangs When Sending Files
When transferring files with Netcat, it’s possible for one side to hang indefinitely, especially if the sender exits too early or the listener wasn’t ready in time.
Common causes include:
- The listener (
-l) wasn’t running before the sender connected. - The sender disconnected without closing the stream properly.
- The shell redirection wasn’t configured correctly.
How to fix it:
-
Always start the listener first, then initiate the sender.
-
Use verbose mode (
-v) on both ends to confirm connection establishment. -
Ensure shell redirection is correct:
- # Receiver
- nc -l 4444 > received_file
- # Sender
- nc example.com 4444 < original_file
-
For larger files or long transfers, consider adding
-q 1on the sender to close the connection after 1 second of EOF:- nc -q 1 example.com 4444 < original_file
By understanding and recognizing these common issues, you can troubleshoot Netcat more effectively and use it with greater confidence in both testing and production environments.
FAQs
1. How do I test a TCP port with Netcat?
To test whether a TCP port is open and accepting connections, you can use Netcat in client mode by specifying the hostname and the target port:
- nc -v example.com 80
-venables verbose output, so you’ll receive confirmation if the connection succeeds or fails.- If the port is open, Netcat will display a message like
Connection to example.com 80 port [tcp/http] succeeded!. - If the port is closed or filtered, you’ll see an error like
Connection refusedorTimed out.
You can also send a simple payload after the connection is established to verify service responsiveness. For example, to send an HTTP request:
- printf "HEAD / HTTP/1.1\r\nHost: example.com\r\n\r\n" | nc example.com 80
This is useful for quickly checking the availability of services such as HTTP, SSH, SMTP, or any custom TCP-based application.
2. How do I test UDP connectivity with Netcat?
To test UDP connectivity, use the -u flag to switch Netcat into UDP mode:
- nc -u -v example.com 53
UDP is connectionless, so you won’t get an acknowledgment by default. Even if the packet reaches the destination, Netcat may display no output at all.
For more accurate results when testing UDP:
-
Use a service that you know responds to UDP traffic (like a DNS server on port
53). -
Combine Netcat with
tcpdumporWiresharkon the receiving system to monitor packet arrival:- sudo tcpdump -n udp port 53
-
To simulate a response, run Netcat in UDP listening mode on another machine:
- nc -u -l 4444
Then send a UDP packet from the client side:
- echo "hello" | nc -u example.com 4444
UDP testing is inherently less predictable than TCP, so be prepared to validate results through multiple layers.
3. What’s the difference between TCP and UDP in Netcat?
The main difference lies in the nature of the underlying protocols:
| Feature | TCP (Default) | UDP (-u option) |
|---|---|---|
| Connection type | Connection-oriented | Connectionless |
| Delivery guarantee | Reliable (guarantees delivery/order) | Best effort, no guarantee of delivery |
| Feedback | Clear success/failure messages | Usually silent; no confirmation |
| Use cases | HTTP, SSH, FTP, SMTP, file transfers | DNS, VoIP, streaming, low-latency protocols |
In Netcat:
- TCP is used by default and provides feedback about connection status.
- UDP requires the
-uflag and will often give no output unless you explicitly send or receive a response. - Netcat handles both protocols in a similar syntax, but behavior differs significantly depending on the transport layer.
Understanding the nature of each protocol will help you use Netcat more effectively in the right context.
4. Is Netcat safe to use in production?
Netcat is a powerful tool, but it should be used with caution in production environments.
Safe Use Cases:
- Internal debugging on isolated networks
- Temporary file transfers between trusted systems
- Service testing within a secure environment
- Automation in development workflows
Risks and Concerns:
- No encryption: Data sent using Netcat is in plain text, including passwords and files.
- No authentication: Anyone who connects to a listening Netcat port can send or receive data.
- Potential misuse: Some attackers use Netcat to create reverse shells or exfiltrate data. For this reason, some security tools flag Netcat as a potential threat.
Best Practices:
- Avoid exposing Netcat listeners to public networks.
- Use firewalls to control access to Netcat ports.
- For secure production transfers, consider using
ncatwith SSL (--ssl) or switch to tools likesocatorOpenSSH.
While Netcat itself is not malicious, its lack of built-in encryption and authentication makes it unsuitable for secure or production-facing environments without additional safeguards.
5. How can I transfer an entire directory using Netcat?
Netcat does not support directory transfers natively, but you can combine it with the tar command to archive and send a directory’s contents over a TCP connection.
-
On the receiving machine, run:
- nc -l 4444 | tar xzvf -
This command listens for an incoming connection and extracts the tarball data it receives from standard input.
-
On the sending machine, navigate to the target directory and run:
- tar -czf - * | nc example.com 4444
This creates a compressed tar archive of the current directory and sends it through Netcat to the receiver.
Using this method, you can quickly and efficiently copy entire directory structures between systems without needing scp or rsync.
6. Can I use Netcat to create a simple chat between two machines?
Yes, Netcat can be used to create a basic peer-to-peer chat by connecting two terminals over TCP.
-
On one machine, start listening:
- nc -l 4444
-
On the second machine, connect to it:
- nc example.com 4444
Once the connection is established, anything typed into either terminal will be echoed on the other. Each user can send messages interactively, and the session will remain active until one side closes it.
While this chat implementation is very basic (no message tags, timestamps, or multi-user support), it’s a great demonstration of Netcat’s ability to establish bi-directional TCP streams.
7. Does Netcat support IPv6 connections?
Yes, most modern Netcat implementations, including netcat-openbsd and ncat, support IPv6.
To force Netcat to use IPv6, use the -6 option:
- nc -6 example.com 80
This attempts a connection to the specified host using its IPv6 address. If the host only resolves to an IPv4 address, the connection will fail.
To confirm the address resolution and connection path, you can combine it with the -v (verbose) flag:
- nc -6 -v example.com 80
Ensure your system and network are configured for IPv6, and the target server is reachable over IPv6, before attempting this.
Conclusion
You should now have a solid understanding of what Netcat can be used for and how it fits into a variety of networking scenarios. This versatile tool excels at helping you diagnose issues, test connectivity, transfer files, and establish basic TCP or UDP communication between systems.
In this guide, we covered Netcat’s core syntax and usage patterns, including port scanning, file transfers, setting up simple web servers, and basic chat communication. We also explored differences between Netcat variants, real-time debugging techniques, how to interpret silent failures, especially with UDP, and how Netcat compares to tools like telnet and socat. Finally, we covered troubleshooting tips and detailed FAQs to help you resolve common issues and use Netcat more effectively.
Netcat simplifies low-level network interactions by giving you transparent, scriptable access to sockets. While not suited for secure or production-grade deployments, it remains an essential utility for quick tests, diagnostics, and network experimentation.
Thanks for learning with the DigitalOcean Community. Check out our offerings for compute, storage, networking, and managed databases.
About the author(s)
Former Senior Technical Writer at DigitalOcean, specializing in DevOps topics across multiple Linux distributions, including Ubuntu 18.04, 20.04, 22.04, as well as Debian 10 and 11.
With over 6 years of experience in tech publishing, Mani has edited and published more than 75 books covering a wide range of data science topics. Known for his strong attention to detail and technical knowledge, Mani specializes in creating clear, concise, and easy-to-understand content tailored for developers.
Still looking for an answer?
This textbox defaults to using Markdown to format your answer.
You can type !ref in this text area to quickly search our full set of tutorials, documentation & marketplace offerings and insert the link!
Amazing. I’d heard of netcat and wanted to get started with it but did not know where to begin. This is a perfect intro, thanks!
Good article, but you have formatting issues from somewhere in “How To Send Files through Netcat”.
great intro to netcat, thanks! I use nmap for doing port scanning, but its nice to be able to do it with netcat as well, since nmap is often not included in the base linux packages.
nice article you covered lot of variants, can you please also show an example to listen( nc -lu <port_num>) on specific udp port. That could be helpful for the first readers.
Nice article. One point worth mentioning.
When using netcat as a simple web server, you have this command written: netcat -l 8888 < index.html
You actually need to specify the port in the command, or else it won’t work. Try this instead. netcat -lp 8888 < index.html I found this solution to work.
Keep up the good work!
This comment has been deleted
- Table of contents
- Introduction
- Key takeaways
- General Syntax
- What are the differences between `nc`, `ncat`, and `netcat-openbsd`?
- How to use Netcat for port scanning
- How to communicate through Netcat
- How to use Netcat in real-time debugging scenarios
- How To Send Files through Netcat
- How To Use Netcat as a Simple Web Server
- Interpreting No Output or Connection Timeouts (Especially for UDP)
- Comparing Netcat with Modern Tools Like `socat` or `telnet`
- How to troubleshoot common Netcat errors and issues
- FAQs
- Conclusion
Deploy on DigitalOcean
Click below to sign up for DigitalOcean's virtual machines, Databases, and AIML products.
Become a contributor for community
Get paid to write technical tutorials and select a tech-focused charity to receive a matching donation.
DigitalOcean Documentation
Full documentation for every DigitalOcean product.
Resources for startups and AI-native businesses
The Wave has everything you need to know about building a business, from raising funding to marketing your product.
Get our newsletter
Stay up to date by signing up for DigitalOcean’s Infrastructure as a Newsletter.
New accounts only. By submitting your email you agree to our Privacy Policy
The developer cloud
Scale up as you grow — whether you're running one virtual machine or ten thousand.
Start building today
From GPU-powered inference and Kubernetes to managed databases and storage, get everything you need to build, scale, and deploy intelligent applications.
