- Log in to:
- Community
- DigitalOcean
- Sign up for:
- Community
- DigitalOcean

Introduction
Although the command line is a powerful tool that can allow you to work quickly and easily in many circumstances, there are instances where a visual interface is helpful. If you are configuring many different services on one machine, or administering portions of your system for clients, tools like ISPConfig can make this a much simpler task.
ISPConfig is a control panel for your server that allows you to easily configure domains, email addresses, site configurations, and user accounts. We will be installing the panel on an Ubuntu 14.04 server.
Prerequisites
Before we get started, you should have a domain name pointed at the server that you will be using. To find out how to configure your domain name with DigitalOcean, click here.
You will also need a non-root user with sudo privileges. You can learn how to set up a non-root account by following steps 1-4 in our Ubuntu 14.04 initial server setup guide. Log in as this user to get started.
Upgrade the System
The first thing we should do is upgrade the base system. This will ensure that the packages on our system are the newest packaged versions.
We should update our local package index before we do this so that apt knows about the latest package versions:
sudo apt-get update
sudo apt-get upgrade
Our system should now be up to date and we can get going with the rest of the installation.
Verify Hostnames are Configured Correctly
We will start by making sure our hostnames are configured correctly. In this guide, we are going to be assuming that the domain name that we are setting up is server.test.com and the IP address for the server is 111.111.111.111.
We need to verify that our hostname is configured correctly. We should look at our hosts file:
sudo nano /etc/hosts
It may look something like this:
127.0.0.1 localhost server.test.com server
We want to make our hostnames use our public IP address. You can do this by splitting up the line into two lines and pointing the domain name portion to our public IP address:
<pre> 127.0.0.1 localhost <span class=“highlight”>111.111.111.111 server.test.com server</span> </pre>
Save and close the file when you are finished.
We should also edit our hostname file to make sure that it contains the correct domain name as well:
sudo nano /etc/hostname
If your whole hostname is not displayed, modify the value:
<pre> <span class=“highlight”>server.test.com</span> </pre>
You should make sure the system uses the new value by typing:
sudo hostname -F /etc/hostname
Change System Settings
There are a few items that Ubuntu configures in an unconventional way that we need to undo in order for our software to function properly.
The first thing we need to do is disable AppArmor, which is incompatible with ISPConfig. First, we should stop the service:
sudo service apparmor stop
We can also tell it to unload its profiles by typing:
sudo service apparmor teardown
After this is done, we need to tell our server not to start this service at boot:
sudo update-rc.d -f apparmor remove
We can actually delete all of the associated files and packages by typing:
sudo apt-get remove apparmor
Another configuration that we need to modify is the default system shell. Ubuntu uses the dash shell for system processes, but ISPConfig leverages additional functionality that is provided specifically by bash. We can set bash to be the default system shell by typing:
sudo dpkg-reconfigure dash
At the prompt, select “No” to have the utility reconfigure the system shell pointer to use bash instead of dash.
Install Additional Components
Now that we have our base system ready to go, we can begin installing some of the services that ISPConfig can manage and some software that supports ISPConfig.
We will be installing basic LAMP (Linux, Apache, MySQL, PHP) components, mail software, anti-virus scanning software for our mail, and other packages.
We will do this all in one big apt command, so this will be a lot of packages installed at once:
sudo apt-get install apache2 apache2-utils libapache2-mod-suphp libapache2-mod-fastcgi libapache2-mod-python libapache2-mod-fcgid apache2-suexec libapache2-mod-php5 php5 php5-fpm php5-gd php5-mysql php5-curl php5-intl php5-memcache php5-memcached php5-ming php5-ps php5-xcache php5-pspell php5-recode php5-snmp php5-sqlite php5-tidy php5-xmlrpc php5-xsl php5-imap php5-cgi php-pear php-auth php5-mcrypt mcrypt php5-imagick imagemagick libruby memcached phpmyadmin postfix postfix-mysql postfix-doc mysql-server openssl getmail4 rkhunter binutils dovecot-imapd dovecot-pop3d dovecot-mysql dovecot-sieve mailman amavisd-new spamassassin clamav clamav-daemon zoo unzip zip arj nomarch lzop cabextract apt-listchanges libnet-ldap-perl libauthen-sasl-perl daemon libio-string-perl libio-socket-ssl-perl libnet-ident-perl libnet-dns-perl bind9 dnsutils vlogger webalizer awstats geoip-database libclass-dbi-mysql-perl squirrelmail pure-ftpd-common pure-ftpd-mysql snmp
During the installation, you will be asked a few questions. You will be asked to select a language for mailman. Select en (English) to continue. You will also be asked to select and confirm a password for the MySQL administrative user.
Another prompt that you will get is whether to create a self-signed SSL certificate for dovecot. You should select “Yes”. You will have to enter the “commonName” for your SSL certificate. This is just your fully qualified domain name:
server.test.com
For postfix, you will be asked what kind of mail configuration you need. Select Internet Site. You will then be asked to choose the system mail name. You should set this to your domain name as well:
server.test.com
For phpMyAdmin, the software has the ability to automatically configure itself based on your web server. Select “apache2” and press “SPACE” to select that option. Hit “TAB” then “ENTER” to make the selection.
Later on, you will asked whether you wish to configure the database for phpMyAdmin with dbconfig-common. Choose “Yes” here. You will need to enter the password of the MySQL administrator account that you selected above. You can then select and confirm a password for the phpMyAdmin user.
At this point, all of your components should be installed.
Configure the Backend Components
Now that everything is installed, we need to start configuring our services and tools.
Mail Configuration
Let’s start by enabling some functionality in postfix. Open the default configuration file with your editor:
sudo nano /etc/postfix/master.cf
We just need to uncomment some of the lines in this file. Specifically the line that deals with the submission service and the first three option lines beneath, and the smtps service and the first three option lines for that one as well:
submission inet n - - - - smtpd
-o syslog_name=postfix/submission
-o smtpd_tls_security_level=encrypt
-o smtpd_sasl_auth_enable=yes
. . .
smtps inet n - - - - smtpd
-o syslog_name=postfix/smtps
-o smtpd_tls_wrappermode=yes
-o smtpd_sasl_auth_enable=yes
Now, we need to append an additional option under both of these services. It will be the same for each:
<pre> submission inet n - - - - smtpd -o syslog_name=postfix/submission -o smtpd_tls_security_level=encrypt -o smtpd_sasl_auth_enable=yes <span class=“highlight”>-o smtpd_client_restrictions=permit_sasl_authenticated,reject</span> . . . smtps inet n - - - - smtpd -o syslog_name=postfix/smtps -o smtpd_tls_wrappermode=yes -o smtpd_sasl_auth_enable=yes <span class=“highlight”>-o smtpd_client_restrictions=permit_sasl_authenticated,reject</span> </pre>
Save and close the file when you are finished.
Another mail related service that we should configure is mailman, which can handle mailing lists.
We can start off by telling it to create a new list:
sudo newlist mailman
You will be asked to provide the email that will be associated with the list. You will also be asked to select a password.
The script will output a long list of aliases. You should add those to the bottom of the your /etc/aliases file:
sudo nano /etc/aliases
It should look something like this:
<pre> postmaster: root <span class=“highlight”>mailman: “|/var/lib/mailman/mail/mailman post mailman”</span> <span class=“highlight”>mailman-admin: “|/var/lib/mailman/mail/mailman admin mailman”</span> <span class=“highlight”>mailman-bounces: “|/var/lib/mailman/mail/mailman bounces mailman”</span> <span class=“highlight”>mailman-confirm: “|/var/lib/mailman/mail/mailman confirm mailman”</span> <span class=“highlight”>mailman-join: “|/var/lib/mailman/mail/mailman join mailman”</span> <span class=“highlight”>mailman-leave: “|/var/lib/mailman/mail/mailman leave mailman”</span> <span class=“highlight”>mailman-owner: “|/var/lib/mailman/mail/mailman owner mailman”</span> <span class=“highlight”>mailman-request: “|/var/lib/mailman/mail/mailman request mailman”</span> <span class=“highlight”>mailman-subscribe: “|/var/lib/mailman/mail/mailman subscribe mailman”</span> <span class=“highlight”>mailman-unsubscribe: “|/var/lib/mailman/mail/mailman unsubscribe mailman”</span> </pre>
Save and close the file after you’re done. You need to make postfix aware of the aliases you added. You can do that by typing:
sudo newaliases
We can start the mailman service by typing:
sudo service mailman start
Restart the postfix service to enable mail changes:
sudo service postfix restart
While we’re dealing with services, we should also stop and disable spamassassin. ISPConfig calls this as needed and it does not need to be running all of the time:
sudo service spamassassin stop
We can then tell the server to not start it again at boot:
sudo update-rc.d -f spamassassin remove
LAMP Configuration
We need to enable mcrypt functionality in PHP:
sudo php5enmod mcrypt
Another thing we need to do is enable some of the Apache modules we installed.
sudo a2enmod rewrite ssl actions include cgi dav_fs suexec dav auth_digest fastcgi alias
We also need to make some adjustments to some of the Apache configuration files.
One of the modules that we enabled will currently intercept all of our PHP files. We want to stop it from doing this. Open the suphp configuration file:
<pre> sudo nano /etc/apache2/mods-available/suphp.conf </pre> <pre> <IfModule mod_suphp.c> <FilesMatch “.ph(p3?|tml)$”> SetHandler application/x-httpd-suphp </FilesMatch> suPHP_AddHandler application/x-httpd-suphp . . . </pre>
We are going to replace the top block with a single command. It should look like this when you are finished:
<pre> <IfModule mod_suphp.c> <span class=“highlight”>AddType application/x-httpd-suphp .php .php3 .php4 .php5 .phtml</span> suPHP_AddHandler application/x-httpd-suphp </pre>
Save and close the file when you are done.
We are going to have to manually create the symbolic link for the mailman Apache file. We can do that by typing:
sudo ln -s /etc/mailman/apache.conf /etc/apache2/conf-available/mailman.conf
We can then enable that by typing:
sudo a2enconf mailman
If you plan on creating sites that host Ruby files, you should comment out the processing of .rb files in the mime.types file. ISPConfig will handle this itself:
<pre> sudo nano /etc/mime.types </pre> <pre> application/x-rss+xml rss <span class=“highlight”>#</span>application/x-ruby rb application/x-rx </pre>
Save and close the file when you are done.
Now, we can restart Apache to implement our changes:
sudo service apache2 restart
Miscellaneous Configuration
We still need to edit a few more pieces of the system.
Since ISPConfig is often used to subdivide server space for reselling purposes, providing clients with FTP access is often a requirement. We’ve already installed the necessary software, but we need to make some adjustments.
Start by editing the FTP server’s configuration:
sudo nano /etc/default/pure-ftpd-common
We need to make sure our FTP users are confined to a chroot environment so that they do not interfere with the rest of the system. We can do this by changing the VIRTUALCHROOT setting to true:
<pre> VIRTUALCHROOT=<span class=“highlight”>true</span> </pre>
Since FTP is inherently insecure we should at least protect it with TLS encryption. We can set this up by creating a flag file that simply contains the 1 character:
sudo nano /etc/pure-ftpd/conf/TLS
1
Now, we need to create a self-signed certificate that the process can use. We can do this by calling:
sudo openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout /etc/ssl/private/pure-ftpd.pem -out /etc/ssl/private/pure-ftpd.pem
This certificate will be valid for one year. You will have to answer some prompts. Fill them out with your information. The Common Name is perhaps the most important part.
We need to lock down the key file afterwards by typing:
sudo chmod 600 /etc/ssl/private/pure-ftpd.pem
When all of this is done, we can restart the service:
sudo service pure-ftpd-mysql restart
This will allow our FTP daemon to use encryption.
One of the reasons we are getting FTP set up on this system is because we have installed a monitoring daemon called awstats that is configured to expect the existence of this service.
ISPConfig will call awstats as necessary, so it does not need to rely on the cron job that is usually used to poll the server. We can remove this by typing:
sudo rm /etc/cron.d/awstats
Install ISPConfig
We are finally ready to install the actual ISPConfig software.
We can do that by downloading the latest stable version onto our server. As of this writing, the latest stable version that has a direct link available is version 3. We will update the installation once we get everything installed.
Now, you should change to your home directory and download the project using wget:
cd ~
wget http://www.ispconfig.org/downloads/ISPConfig-3-stable.tar.gz
After the download is complete, extract the directory structure and move into the install subdirectory of the extracted folder structure:
tar xzvf ISPConfig*
cd ispconfig3_install/install/
Now, we are ready to install the software. Do so by typing:
sudo php -q install.php
You will be taken through a very lengthy installation processes.
Luckily, the only detail you actually need to enter is your MySQL root password! For every other entry, just press “ENTER” to use the default value and skip ahead.
When you are finished with the installation, go ahead and update to the latest version by typing:
sudo php -q update.php
Again, just press “ENTER” to use the defaults for each command.
When you are finished, you can visit your ISPConfig service by visiting your domain name followed by :8080 in your web browser:
<pre> https://<span class=“highlight”>server_domain_name</span>:8080 </pre>
You will get an SSL warning since we are using self-signed certificates:
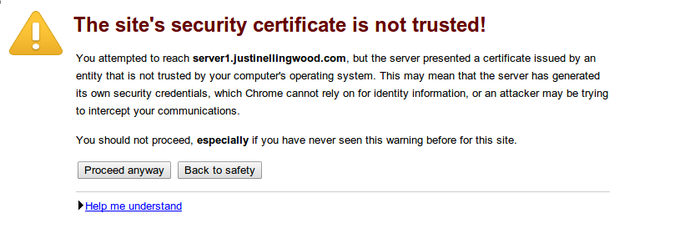
Click “proceed” or “continue” to accept the certificate.
You will be taken to a login screen.

The default username and password are both admin:
Username: admin
Password: admin
Enter those values and you will be taken to the ISPConfig3 interface:

Once you get here, you should change the admin user’s password by clicking on the “System” button, then clicking the “CP Users” link under the “User Management” category of the left-hand navigation menu.
Click on the admin user account in the main window. You will have the option to change the password for the admin user on this page.
Conclusion
You should now have your ISPConfig panel installed and configured. You should be able to manage domains, mail, and accounts from within this interface.
<div class=“author”>By Justin Ellingwood</div>
Thanks for learning with the DigitalOcean Community. Check out our offerings for compute, storage, networking, and managed databases.
About the author
Former Senior Technical Writer at DigitalOcean, specializing in DevOps topics across multiple Linux distributions, including Ubuntu 18.04, 20.04, 22.04, as well as Debian 10 and 11.
Still looking for an answer?
This textbox defaults to using Markdown to format your answer.
You can type !ref in this text area to quickly search our full set of tutorials, documentation & marketplace offerings and insert the link!
Can you please give the code/ instructions for nginx for this part; sudo nano /etc/apache2/mods-available/suphp.conf
<IfModule mod_suphp.c> <FilesMatch “.ph(p3?|tml)$”> SetHandler application/x-httpd-suphp </FilesMatch> suPHP_AddHandler application/x-httpd-suphp . . .
We are going to replace the top block with a single command. It should look like this when you are finished:
<IfModule mod_suphp.c%gt; AddType application/x-httpd-suphp .php .php3 .php4 .php5 .phtml suPHP_AddHandler application/x-httpd-suphp
@Rod Thompson: There isn’t a direct substitution for nginx. Instead of suphp you should use php5-fpm in combination with fcgiwrap. That part is a per-requisite for the mailman apache configuration. In nginx, you’d do something like the following to set up mailman:
<pre> location /cgi-bin/mailman { root /usr/lib/; fastcgi_split_path_info (^/cgi-bin/mailman/[^/])(.)$; include /etc/nginx/fastcgi_params; fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name; fastcgi_param PATH_INFO $fastcgi_path_info; fastcgi_param PATH_TRANSLATED $document_root$fastcgi_path_info; fastcgi_intercept_errors on; fastcgi_pass unix:/var/run/fcgiwrap.socket; }
location /images/mailman {
alias /usr/share/images/mailman;
}
location /pipermail {
alias /var/lib/mailman/archives/public;
autoindex on;
}
</pre>
Though I’d encourage you to stick with Apache for this one. I’m a big nginx fan, but in this case it is a much more forward set up with Apache than nginx.
Hi,
Thanks for the “How-To”.
Would I be correct in thinking it needs to be installed on a new droplet, and not one already in use?
Terence.
As Rob Thompson mentioned, is the there a syntax error in this below as I can’t restart the Apache server because I’m getting an error due to not having a closing “>” <IfModule mod_suphp.c%gt; AddType application/x-httpd-suphp .php .php3 .php4 .php5 .phtml suPHP_AddHandler application/x-httpd-suphp
Thanks
a.tricky.1: Yep, I made an error in creating the “>” html element. It should be fixed above.
terence.milbourn: While it doesn’t explicitly require you to install on a new droplet, that’s usually the best way to ensure that the operation will go smoothly.
I’ve installed all ok but my main domain can’t send or receive emails. I’ve installed everything on domain1.com and all my domains target to the same server and works well (domain2.com, domain3.com, …) but the main domain (domain1.com) can’t receive or send emails neither to itself neither to out. Someone can help me ?
Thanks for the great tutorial. I will certainly try this out. Is there any particular reason for the use of a self signed certificate? I have my certificates signed by digicert and would prefer to use those instead.
@thomashrb: The self signed certs are just to get SSL up and running and running. If you have certs from digicert, that’s even better.
- Table of contents
- Prerequisites
- Upgrade the System
- Verify Hostnames are Configured Correctly
- Change System Settings
- Install Additional Components
- Configure the Backend Components
- Miscellaneous Configuration
- Install ISPConfig
- Conclusion
Deploy on DigitalOcean
Click below to sign up for DigitalOcean's virtual machines, Databases, and AIML products.
Become a contributor for community
Get paid to write technical tutorials and select a tech-focused charity to receive a matching donation.
DigitalOcean Documentation
Full documentation for every DigitalOcean product.
Resources for startups and AI-native businesses
The Wave has everything you need to know about building a business, from raising funding to marketing your product.
Get our newsletter
Stay up to date by signing up for DigitalOcean’s Infrastructure as a Newsletter.
New accounts only. By submitting your email you agree to our Privacy Policy
The developer cloud
Scale up as you grow — whether you're running one virtual machine or ten thousand.
Start building today
From GPU-powered inference and Kubernetes to managed databases and storage, get everything you need to build, scale, and deploy intelligent applications.
